I remember my first home network. I was living in my parents home and ran a null modem cable between two computers with the LapLink Software Package. After that, my home network evolved to 10BASE-2, 10BASE-T and then 100BASE-T. I was the envy of my friends when I purchased a network switch — at the time everyone else used network hubs. My first router was a home built Linux server on the 2.0.x kernel with ipfwadm at the core with an always connected 28.8kbps modem for connectivity.
Network segmentation is a network security technique to give devices only what they need to operate and nothing more. This level of network segmentation is made easy by the Software Defined Network of the Unifi product line by Ubiquiti. While it’s fairly straight forward to do, it’s not by any means intuitive. Maybe some day a company will come up with a home network that is pre-segemented, that is if the concept of network segmentation is still around.
Fast forward to today and software defined networking. All of our devices have very simple to use web interfaces. Who ever needs to use a terminal to configure the network these days? I know it’s been a while for me too.
This simplicity has evolved in response to an ever growing network and the abstractions we need to maintain this network for all of our connected devices.
My home network is not common, it’s definitely an outlier in terms of complexity but it is this way out of necessity. I’ve lived through the days where you can get as many (free) real static IP addresses you want for devices to be fully discoverable on the internet. I’ve lived through Windows being attacked on a regular basis and it being used as a vector to take over the rest of network. Heck, I’ve had security cameras breached because they were running an out of date version of Linux and had a poor implementation of UPnP.
Before settling on Uniquiti, I was heavily vested in dd-wrt. It was a good platform and very flexible but easy to use it was not. I wanted to do things that were just not feasible with that platform.
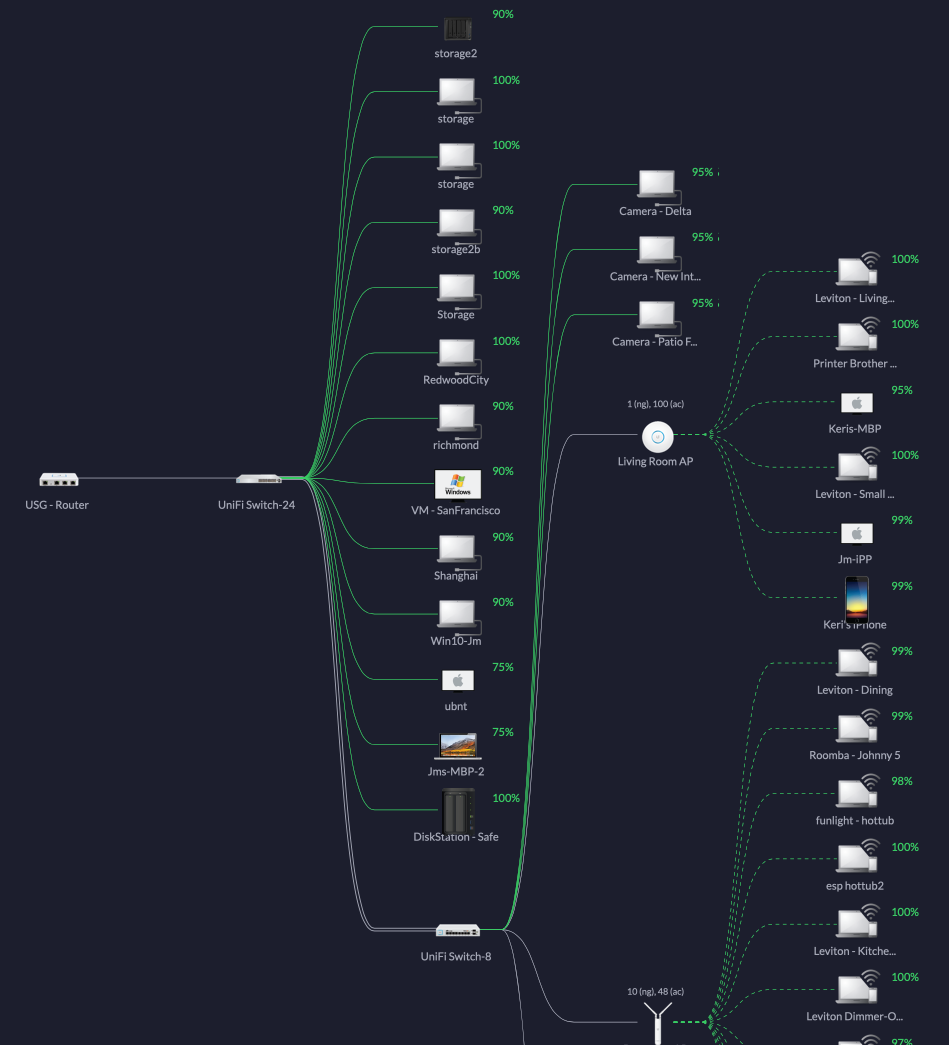
Depending on time of day and day of the week, there are anywhere between 40 and 60 devices on my home network online at any one time. While I completely trust some of these devices, others I do not and there is no way I can stay on top of all the devices at all time.
Table of Contents
Why Segment?
All this talk about segmentation needs to start with the question “Why”. There’s no hiding the fact that this is a lot of up front work, but if you have more than a dozen devices on your network — do consider it.
Segmentation has two main benefits:
Improved Network Performance
Having multiple network segments reduces congestion by reducing the number of hosts on a network and by reducing network broadcast storms caused by having a large number of devices on the network. Have you ever looked at the lights on a network switch and notice that they sometimes blink all at once? That’s a sign that that network is experiencing a lot of broadcast traffic. Check out the article by Auvik on the topic of Boadcast Storms if you’d like to learn more.
Improved Security
Even without implementing any firewall rules, segmentation will contain broadcasts to the same network. This will reduce the ability for hackers to find your devices because the devices inside one network are not easy to identify from another network.
There’s also the reduced attack surface from both malicious and non malicious causes. Imagine if you have 100 devices and equally distribute that those over 4 networks. An attacker now has 75% less of a surface to attack.
There are many other security benefits too, but those are all variants of the two above.
Let’s Talk About Security
This is not intended to be “the more secure network in the world” but it is significantly better than most alternatives. The security in place must not be a hinderance to usability. If usability is sacrificed, then the security process will be ignored.
For the home, it has to be easy to use for both the administrator (that’s you and me) and everyone else.
Most home networks have a single, flat, network where everything resides. Even without any firewall rules, grouping like devices will reduce the risk of one group of devices affecting another group of devices. As an example, let’s say a security camera is compromised — segmentation reduces the likelihood that it will affect any local servers or other personal devices.
IoT Security
Internet of Things devices are a varied lot. Without doing a deep analysis into what they’re actually doing, it’s difficult to know how to best protect them from the world and from each other. We can classify IoT devices into three levels. I’m sure someone can come up with more granular levels, but let’s keep it easy.
IoT Level 1 – Internal and External Connections – Connections methods are extremely varied. They may reach out to the internet for cloud services, may act as a bridge between internal devices and they may also be interfaced with people in the house either directly or through mobile devices. Examples of this would be the Apple TV or Android TV.
IoT Level 2 – External Connections Only – Initiates outbound connections to Cloud services and does not directly communicate with internal devices. Examples of this are devices like the Nest Thermostat, Roomba and Instant Pot.
IoT Level 3 – Internal Connections Only – These devices only work within the local network and has no practical need to directly connect with Internet. Examples of this include HomeKit Switches and Outlets, Network Printers and some Weather Stations. Also included are Security Cameras that interface with a Local Network Video Recorder. but not Security Cameras that interface with Cloud Network Recorder, like the Ring or Nest Security Cam.
While it would be best to identify just how much access a device needs, it also takes a lot of analysis to determine how the device has been designed to work. I have decided to group level 1 and level 2 together into a single vLan and put as few devices there as possible. Some day that may be improved, but for now let’s keep it easy.
Wireless Security
For the network with personal devices, we use WPA2/Enterprise to secure the network which was chosen selected because Windows, Mac and mobile platforms store the WPA2/Personal credentials locally and are generally very accessible. This means that the network password can be looked up by anyone with little effort. On mobile devices, especially on Apple devices, they openly share network credentials with anyone in their address book who is near by. With WPA2/Enterprise, authentication is first performed using a username / password. After the initial hand shake, the device persists the connection by means of cryptographic keys. That can not be easily shared.
WPA2/Personal is actually good at keeping everyone out. Unfortunately, not many IoT devices support WPA2/Enterprise. While the Apple Watch supports WPA2/Enterprise, I have yet to find an inexpensive IoT device that does support WPA2/Enterprise.
Segmentation
For a refresher on Network Segmentation, please checkout the page on Wikipedia on the topic.
On the most basic level — The network has to both be easy to use while not limiting anything I want to do. Any security must be completely transparent to anyone and anything using the network.
Our network is segregated in a few VLANs and accessible over four Wireless Networks.
Is all this segmentation necessary? With up to 60 devices on the network at any time. I don’t have time to manage each and every one of them and who knows what’s going on with the IoT devices. If something starts to behave poorly, I’ll eventually chase it down but an easy “OFF” button will come in handy. Maybe micro segmentation trickle down to the consumer level.
VLAN
The segments are created to group similar devices and give them only the amount of access they need. In addition to the firewall rules, a we have a local DNS server running PiHole with aggressive filter rules to block known malicious domains and those hosting advertisements. The local DNS serves all segments except the Untagged (LAN) segment, providing a bit of application level security.
At some point, I may create another VLAN for “Partially Trusted” IoT devices, but I don’t yet know how that may be configured. It’ll probably just open HTTP/80, HTTPS/443, MQTT/1883 and MQTTS/8883. This would be for devices like the Garage Door Opener, the Roomba or the Nest Thermostat.
| VLAN ID | Name | Firewall | Notes |
| 1/Untagged | Remote User VPN | All users who connect to the VPN server are placed on this network. It’s best to put remote users on their own network so they will be less able to discover nearby devices if the connection is compromised. | |
| 1/Untagged | LAN | Nothing added | This is the management network. Dedicated to core servers and core networking gear. |
| 100 | Family | Nothing added | Vast majority of our personal devices go here. Phone, Tablets, Laptops, etc. |
| 200 | Guest |
|
For guests that need access to the internet but no access to our internal network.
|
| 300 | Untrusted_IoT |
|
Secure network for untrusted IoT devices. These are devices that have no reason to have direct internet connectivity. These devices include light switches, security cameras, printers, oscilloscopes, lab power supplies, etc.
I may create a rule to block connections from this network to other networks that were not first initiated from outside the network. |
| 400 | Trusted_IoT | Nothing added | IoT devices that need access to the Internet — like the Apple TV, Android TV, Nest, weather stations, Garage Door Opener or Roomba.
I considered having a rule to stop devices here from initiating a connection to other networks, but then if that were the case — the Apple TV will be unable to act as a HomeKit server for the home. |
| 1000 | 10gbe | Nothing added | Physical segment for devices on 10gbe connection. Even though it’s on separate hardware, all the traffic on that network is tagged for the eventuality when I have a core switch that supports both 1gbe and 10gbe. All devices on this segment is configured to use jumbo frames. |
WLAN
For this network there isn’t a 1:1 mapping between VLAN IDs and WLAN (Wireless LAN) names, but it’s close. Please note that these are not the names of my actual network.
Unifi support up to 8 SSIDs per Access Point, but best practice is to use only 4. If more than 4 are used, that will disable the ability to create Wireless Mesh Networks. All my Access Points are hard wired but they do fall back to use a mesh network the event the physical cable is damaged or disconnected.
| SSID | VLAN | Security | Notes |
| PersonalDevices | 100 | WPA2/Enterprise | Vast majority of our personal devices go here. Phone, Tablets, Laptops, etc. |
| Guest | 200 | WPA2/Personal | For guests that need access to the internet but no access to our internal network. |
| Untrusted_IoT | 300 | WPA2/Personal | Secure network for untrusted IoT devices. Devices here are not have an inbound or outbound route to the Internet. Devices in this category include our light switches and security cameras. |
| Trusted_IoT | 400 | WPA2/Personal | This is for devices that must have a connection to the public internet. Devices in this category include the Nest Thermostat and the Roomba |
Firewall Rules
A separate article on how to create these rules is currently in progress. Message me in the notes below if you need instructions sooner or would like me to notify you when the article is ready.
Updates
- 2020 04 02 – New section “Why segment?”
- 2020 04 29 – Updated VLAN section. New section on Security.
- 2020 04 27 – Initial Version
Very interesting. I’m looking forward to part 2.
I’d love to see the firewall rules that accomplish this
Pls notify me. Would love to replicate this on our home network.
Would love to see how you configure your rules – my planned network setup is extremely similar.
I have the new article about 1/3 done in draft. I expect to have more time on it this weekend.